<ph type="x-smartling-placeholder"></ph>
在 GitHub 上查看源代码
Wireshark 是一种开源工具,可以解码 Thread 中的网络协议 例如 IEEE 802.15.4、6LoWPAN、IPv6、MLE(网状链路建立)、UDP、 和 CoAP。
Pyspinel Sniffer 工具连接到 Thread NCP 或 RCP 设备并对其进行转换 混用数据包嗅探器中,可生成 pcap(数据包捕获)流, 或直接传送到 Wireshark 中。
如需将 Wireshark 与 Pyspinel 搭配使用,请参阅 下一步。您还需要配置 Wireshark 才能正确显示线程数据包 并接收 RSSI 测量结果。
安装 Wireshark
Linux
打开终端并运行以下命令,以下载并安装 Wireshark:
sudo add-apt-repository ppa:wireshark-dev/stablesudo apt-get updatesudo apt-get install wireshark
我们建议以非 root 用户身份运行 Wireshark。为此,请重新配置该软件包:
sudo dpkg-reconfigure wireshark-common
当您看到询问“Should non-超级用户能够捕获数据包?”的对话框时,
选择 Yes,然后添加 wireshark 用户并更新文件权限:
sudo adduser $USER wiresharksudo chmod +x /usr/bin/dumpcap
macOS 和 Windows
下载并安装 Wireshark。为您的操作系统优化安全性, 请参阅 Wireshark - 关于捕获权限的平台特定信息。
配置 Wireshark 协议
要配置协议,请在 Wireshark 中选择 Preferences...,然后展开 协议部分。
6LoWPAN
从协议列表中选择 6LoWPAN,然后验证或更改以下内容 设置:
- 取消选中根据 RFC 4944 派生 ID。
- 使用目标线程的 Mesh Local Prefix 更新 Context 0 。
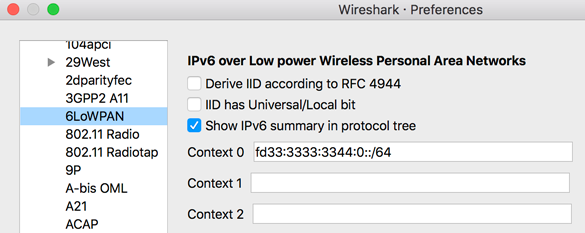
Wireshark 使用上下文配置来解析压缩的 IPv6 地址, 正确显示 IPv6 来源和目标地址。
如需显示网关上配置的其他网状前缀的地址, 使用这些前缀更新其他上下文 ID。
如需获取特定网状网前缀的上下文 ID,请查看 Thread 网络数据 任何 MLE 数据响应消息中的 TLV。例如:
Context 1: fd00:7d03:7d03:7d03::/64
CoAP
从协议列表中选择 CoAP,并设置 CoAP UDP 端口 61631。这可确保显示 TMF 消息(如地址请求)。
IEEE 802.15.4
从协议列表中选择 IEEE 802.15.4,然后验证或更改 以下设置:
- 将 802.15.4 Ethertype(十六进制)设置为“0x809a”。
- 将安全套件设置为“AES-128 Encryption, 32-bit Integrity” 保护”。
点击解密密钥旁边的修改...按钮 添加用于数据包解密的 Thread 网络主密钥。
- 点击 + 以添加解密密钥。
- 在 Decryption key(解密密钥)列中输入 Thread 网络主密钥。
- 输入“1”用作解密密钥索引。
从 Key hash 列列表框中选择 Thread hash。
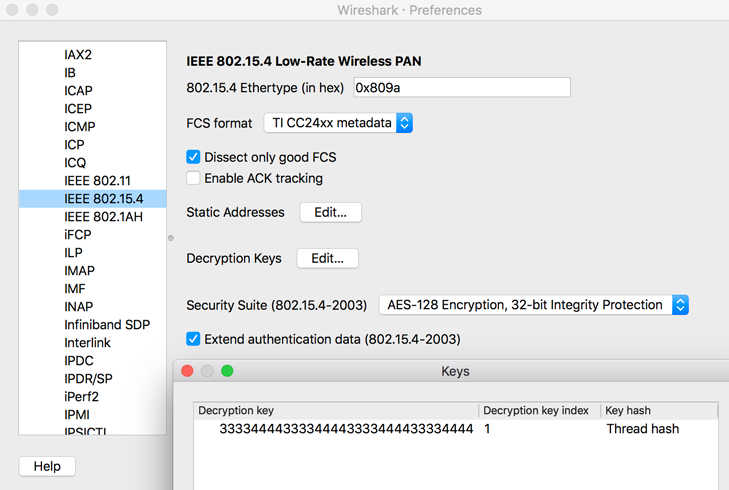
点击确定以保存解密密钥。
会话
从协议列表中选择 Thread,然后验证或更改以下设置 设置:
- 输入“00000000”(针对线程序列计数器)。
- 取消选中使用 PAN ID 作为主密钥的前两个八位字节。
- 选中自动获取线程序列计数器。
点击确定按钮以保存所有协议更改。
某些 Thread 流量可能会作为 ZigBee 协议进行分析。正确 显示这两个协议,请修改 Wireshark 中已启用的协议:
- 在 Wireshark 中,转到 Analyze,然后点击 Enabled Protocols。
取消选中以下协议:
- LwMesh
- ZigBee
- ZigBee 绿色电能
配置 Wireshark RSSI
如需在 Wireshark 中显示 RSSI,请执行以下操作:
- 选择偏好设置...并展开协议部分,然后点击 IEEE 802.15.4。
设置 FCS 格式:
点击 OK 保存,然后返回到 Preferences 菜单。
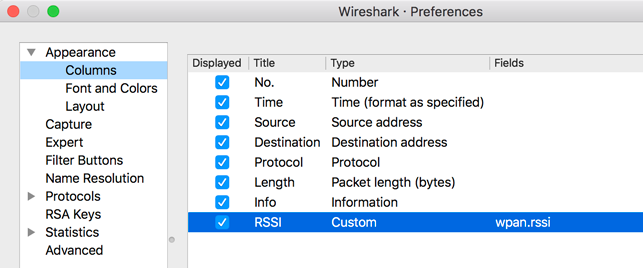
从偏好设置中,选择外观,然后选择列。
添加新条目:
- 标题:RSSI
- 类型:自定义
- 字段:wpan.rssi